• Expertise in Identity & Access Management
• Vendor-agnostic architecture approach
• Secure enterprise-grade implementation
• Integration with PAM, MFA, and Zero Trust architectures
• End-to-end deployment and knowledge transfer
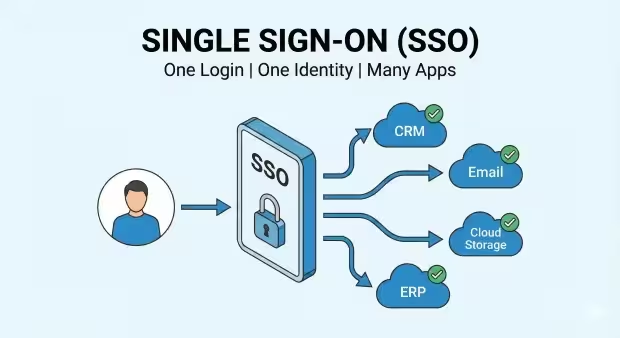
Secure Access to All Applications with a Single Login
Enable your workforce to access all business applications securely with Single Sign-On (SSO). Reduce password fatigue, strengthen security, and simplify identity management across your entire organization.
The Challenge of Managing Multiple Logins
Modern organizations rely on dozens — sometimes hundreds — of applications. Without centralized authentication:
• Employees struggle with password fatigue
• IT teams waste time resetting passwords
• Security risks increase due to password reuse
• Access management becomes difficult to control
Managing identities across multiple systems without a unified solution can create significant operational and security challenges.
Key Benefits of Single Sign-On
Improved Security
Centralized authentication allows organizations to enforce strong access policies and integrate advanced security controls such as multi-factor authentication (MFA) and conditional access.
Better User Experience
Employees sign in once and access all applications without repeated logins, improving productivity and reducing frustration.
Reduced IT Workload
Password resets are one of the most common IT helpdesk requests. SSO significantly reduces these incidents.
How Single Sign-On Works
A user logs in through a centralized identity provider.
The identity provider authenticates the user securely.
The system generates a trusted authentication token.
The user can access all connected applications without logging in again.
This process ensures secure, seamless access across cloud and on-premise applications.
Our Implementation Approach
Our SSO Implementation Services
We help organizations design and deploy enterprise-grade SSO solutions tailored to their environment.
Our services include:
• Identity architecture design
• Integration with cloud and on-prem applications
• Secure authentication policy configuration
• MFA and Passwordless authentication integration
• Identity governance and access monitoring
Our goal is to deliver secure, seamless identity access across your entire infrastructure.
Why Organizations Trust HelixQ for SSO
Secure Your Most Critical Access Points Before They Become Breach Vectors.
Schedule a confidential discussion to assess your privileged access risk posture.

