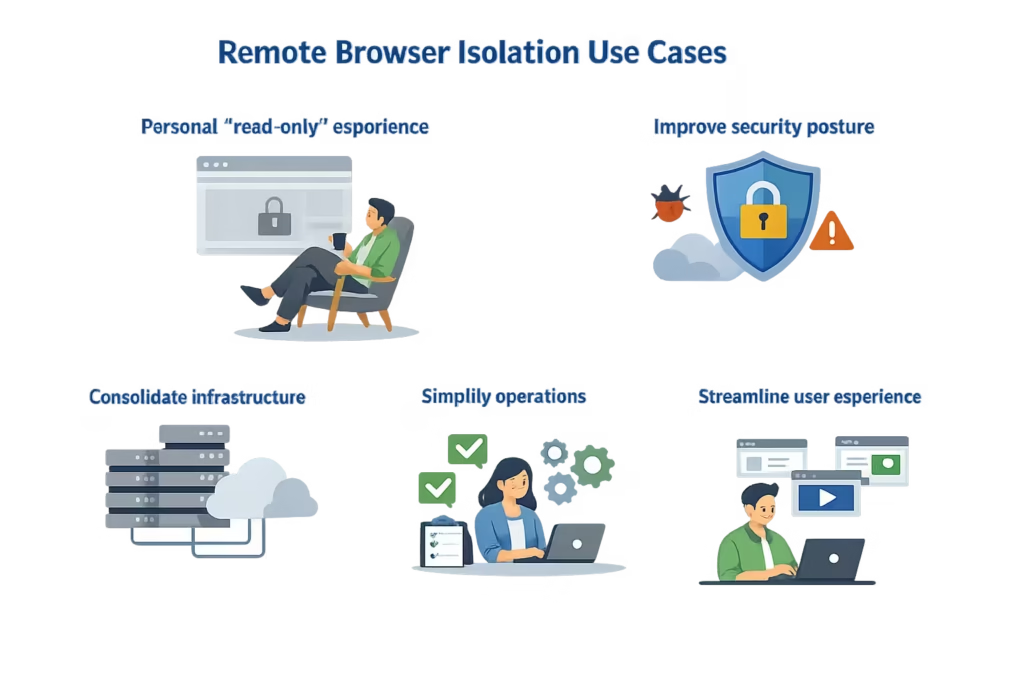
- Personal “read-only” experience
- Improve security posture
- Consolidate infrastructure
- Simplify operations
- Streamline user experience
Browse the Web Safely with Remote Browser Isolation
Safely isolate risky websites and personal applications, plus apply threat and data protection on file activity. RBI delivers seamless safe viewing and ensures no website code executes on end-user devices.
Web Browsing Is a Major Threat Vector
Employees access the internet constantly — for research, communication, and daily operations. However, this creates significant security risks:
• Phishing websites targeting user credentials
• Malware downloads and drive-by attacks
• Zero-day browser exploits
• Malicious scripts embedded in web pages
• Users accessing unknown or risky websites
Traditional security tools attempt to block threats — but not all threats can be detected in advance.
Benefits of Remote Browser Isolation
Protection Against Zero-Day Threats
Unknown and advanced threats are contained in an isolated environment.
Phishing Protection
Users can safely access suspicious links without risk.
Endpoint Protection
No malicious code reaches the user’s device.
Secure Access to Untrusted Websites
Employees can browse freely without exposing the organization to risk.
Reduced Attack Surface
Eliminates browser-based attack vectors.
What is Remote Browser Isolation (RBI)?
Remote Browser Isolation is a security approach that executes web browsing sessions in a remote, isolated environment instead of on the user’s device.
RBI isolates uncategorized and risky websites. Known safe sites are allowed, known bad sites are blocked, and risky websites are isolated for safe viewing all within one cloud platform, one console, and one policy engine.

How Remote Browser Isolation Works
- A user attempts to access a website.
- The request is routed to a remote isolation environment.
- The website is executed in a secure container.
- Only a safe visual representation is streamed to the user.
- Any malicious code remains isolated and is destroyed after the session ends.
This ensures complete separation between web content and the user’s device.

Remote Browser Isolation Use Cases
Why Organizations Work With Us
• Expertise in Zero Trust and web security
• Integration with SWG, CASB, and ZTNA solutions
• Vendor-aligned implementation with leading platforms
• Focus on both security and user experience
• End-to-end deployment and optimization
We help organizations eliminate web-based threats without impacting productivity.
Secure Your Organization’s Internet Access
Protect your users, applications, and data from modern web threats with a Next-Generation Secure Web Gateway.

