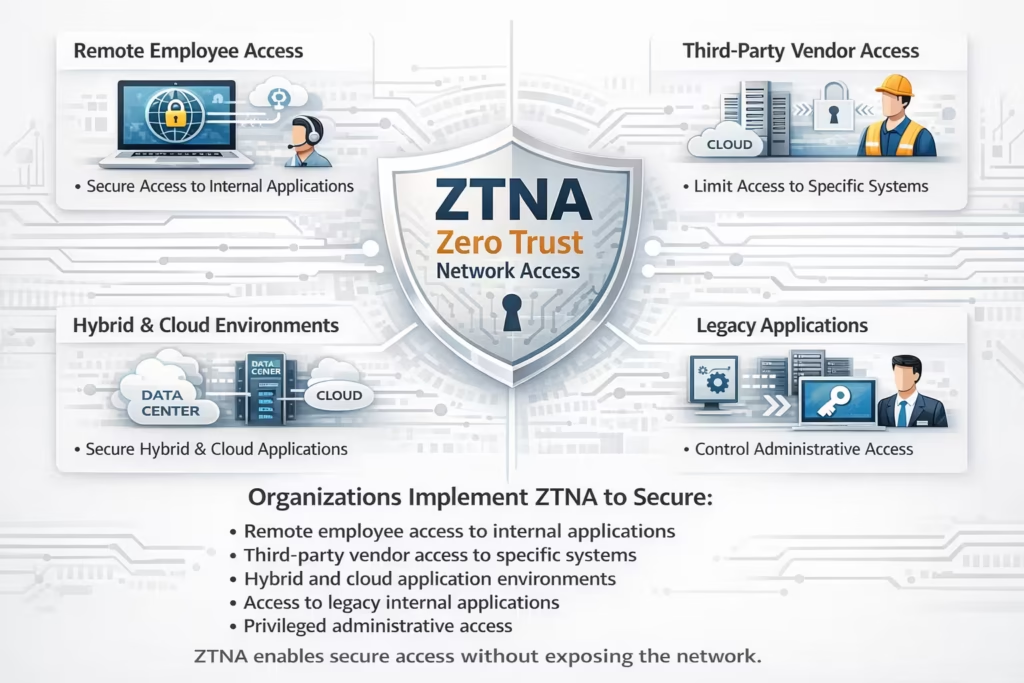
Organizations implement ZTNA to secure:
• Remote employee access to internal applications
• Third-party vendor access to specific systems
• Hybrid and cloud application environments
• Access to legacy internal applications
• Privileged administrative access
ZTNA enables secure access without exposing the network.